Join Us on Apr 30: Unveiling Parasoft C/C++test CT for Continuous Testing & Compliance Excellence | Register Now
Jump to Section
MISRA C/C++ Code Checking
The MISRA standards are benchmarks used across several industries to measure the source code standards written by developers. Read on to discover how Parasoft's static analysis and SAST solutions can help you meet MISRA compliance requirements.
Jump to Section
Jump to Section
MISRA is the legendary coding standard against which development teams measure a large portion of today’s software. But exactly what is MISRA?
- How did MISRA develop?
- How do C and C++ developers gauge standards against it?
- How do they know they’re in compliance with MISRA guidelines?
In this piece, we examine the compelling background of how MISRA came to be. We also answer the above questions and reveal how MISRA helps C++ and C code programmers write code efficiently while addressing current safety and security concerns.
Specifically, we look at:
- MISRA definition and background
- MISRA rules and guidelines
- Compliance
- Reporting
- Use with legacy code
What Is MISRA?
The MISRA standards contain coding guidelines and rules for writing software. The automotive, aerospace and defense, medical, industrial automation, and railway industries, among others, use the standard to help their developers write source code that ensures safety, security, and reliability in the software.
Because embedded software engineers use the C and C++ programming languages to write code for safety-critical software, the creators of the MISRA standard built them for coders who use these two languages.
Background
The Motor Industry Software Reliability Association (MISRA) consortium is comprised of various companies sharing their C and C++ coding best practices. It’s similar to ISO (International Standards Organization) and IEC (International Electrotechnical Commission), which set general industry compliance guidelines like standards for the development of electric/electronic systems.
ISO 26262, published in 2011, is the international standard for certifying the safety of electronics on-road vehicles. Software systems that have achieved ISO/IEC compliance can be certified by verification authorities as safe.
MISRA, a consortium of automotive-related industries, developed its first guidelines in 1998, MISRA C:1998. The consortium came together as a result of the UK Safety Critical Systems Research Programme, which the UK government instituted to address some of the challenges that the automobile industry faced due to the increased use of software in the manufacture and operation of vehicles. Some of the original industries that helped develop the standard, all of whom are also currently active steering-committee members, included:
- Bentley Motors
- Delphi Diesel Systems
- Ford Motor Company Ltd
- Horiba Mira Ltd
- Jaguar Land Rover
- Protean Electric Ltd
- Ricardo PLC
- The University of Leeds
- Visteon Engineering Services Ltd
- ZF TRW
Although the consortium originally created the standard for the automotive industry, other embedded industries have adopted the standard, including those that use embedded technology that connects devices like Internet of things (loT) and medical IoT systems.
The How and Why of MISRA
In the early 1990s, electronics were becoming more and more important in automobiles. So too was the embedded software that was an integral part of these electronics. Thus, engineers and manufacturers began to realize that the reliability of the software was vitally important, for both safety and commercial reasons. The challenge is even greater today because software for a single car can involve in excess of 100 million lines of coding!
Software in Cars and Trucks
Automotive manufacturers use software in engine and powertrain operations. It monitors and provides the correct amount of fuel in ICEs (internal combustion engines) and it supplies data to the ECM (engine control module, sometimes called an ECU, or engine control unit). This is the main automotive computer that gathers information about fuel consumption, the power the engine generates, emissions, and other vital engine-related data essential for safe and efficient driving. Electric vehicles (EVs) and hybrid vehicles have similar software requirements related to the engine and powertrain.
Manufacturers also employ software to operate onboard computers for the ubiquitous sensors on current vehicles, including door and window monitoring, climate control systems, and parking and traffic sensors. They also use them in safety-critical systems like airbags and ABS.
More operation-related software is certainly in the future of road vehicles, with engineers and designers devoting serious attention to self-driving capabilities, improved energy efficiency, and enhanced safety.
Beyond the Motor Industry
Industries throughout the world accept the MISRA C rules for writing safety- and security-critical C code. The rules and guidelines inspire confidence because they’re readable, concise, and focus on essentials.
While applying the MISRA standard does not guarantee that software is free of security and quality problems, it helps software engineers write code that is safer, more robust, more portable, and easier to maintain.
MISRA guidelines also address security vulnerabilities but other coding standards like CERT C specifically tackle security vulnerabilities written into code.
MISRA Coding Standards for Functional Safety
Today, development teams employ coding standards as a method to define, manage, and utilize a group of coding practices, with the primary objective of consistency. The main aim of a coding rule is to limit the incorrect use of the language so it prevents the developer from doing things that are “wrong” and can be potentially dangerous.
Developers can avoid many defects in software by adopting sensible language-use restrictions. This also results in style uniformity, which is valuable as a discipline in a software project.
Versatility and Vulnerability of C and C++
The versatility aspect of the C and C++ languages allows a developer to write code that can be unintentionally incorrect and possibly dangerous. It’s easy for him or her to write code that adheres to the requirements of the language’s standard but this, nonetheless, can result in undesirable behavior and program crashes. For example, code that accesses memory beyond the parameters of an arithmetic process or of an array that results in memory or boundary violations.
It’s important to identify these potential problems. However, the aim of MISRA is to prevent problems, not just identify them. A compiler can detect some of them but using a dedicated analysis tool is more effective.
The MISRA standard emphasizes that adhering to coding rules is only one component of developing software successfully. Developers must integrate each programming project into a disciplined engineering setting that includes methodical development workflows and applies proven in-use validation tools.
Commonly Used MISRA C and C++ Language Guidelines and Rules
Each MISRA standard embodies a set of coding parameters and rules plus support materials. The support materials are a supplemental part of the standard and provide important background information essential for any programmer who wants to obtain compliance.
Let’s look at the C and C++ MISRA coding standards and brief descriptions.
MISRA C 2012. MISRA C 2012 was released in 2013. It drew on experience from interaction with thousands of organizations and best practices from software engineers to provide the best coding guidelines for the C programming language.
The first edition of the standard was MISRA C 1998, evolving over the years to MISRA C:2004 and then MISRA C:2012. Initially, the standard provided support for C90 and evolved to extend its guidelines in support of C99, C11, and C18. MISRA C 2012 also made a number of improvements that lessened the complexity and cost of compliance.
- MISRA C 2012 amendments for safety and security. With the evolving C programming language and to emphasize that MISRA C 2012 was equally valuable in security applications, MISRA published several supporting addendums and amendments to the standard which offered new rules and guidelines for improved coverage of safety and well-known security vulnerabilities.
MISRA C 2023. This is the latest MISRA C standard. It consolidates MISRA C 2012 along with all the amendments and corrigendums that have been released to date. The standard supports the C programming language, versions C90, C99, C11, and C18 languages, and replaces MISRA C 2012.
MISRA C++ 2008. Published in June 2008 and developed in support of C++98 and C++11. Although the C programming language remained the prevailing coding language, this standard spoke to the increased development of C++ applications. However, many businesses opted to standardize using the AUTOSAR C++ 14 coding standard because it supports the C++14 version of the C++ coding language instead of older C11. C++ coding version, officially ISO/IEC 14882:2014 was published in December 2014.
MISRA C++ 2023. AUTOSAR and MISRA joined forces to produce the next generation of the C++ coding standard. MISRA C++ 2023 was released in October 2023 and offers software engineers the ability to scan their modern C++17 and C++20 code for safety and security issues.
MISRA Compliance 2020. This document sets a framework for accomplishing compliance with the MISRA coding standard. It supersedes compliance and process and deviation requirements in previous versions of the standard.
How to Achieve MISRA Compliance Using Static Analysis
The MISRA coding standard furnishes thorough rules and guidelines so companies can protect their applications against runtime errors and software failures and make them less prone to security and safety vulnerabilities.
Compliance with the MISRA standard helps improve syntax, creates code conformity, and facilitates portability. For teams that don’t use static analysis or SAST (static application security testing) solutions or tools, validating compliance can be problematic. Parasoft simplifies the process, which is critical to ensure timely software delivery and coding security.
Getting Started With Static Analysis
To achieve successful compliance, solutions must provide the following.
- Dynamic enforcement by verifying MISRA compliance through static code analysis each time coders modify the software.
- Integration of static analysis into your streamlined CI/CD pipeline with continuous testing that delivers high-quality software quickly.
- Compliance validation by creating high-level, detailed overviews and reports that you can reference quickly.
It’s important to apply MISRA compliance throughout the software development life cycle, including during code implementation for shift left testing and to expedite code reviews. This provides quality improvements as well as progress metrics, ongoing traceability, and enforcement.
Automating documentation and compliance reporting per MISRA Compliance 2020 is a key factor for conserving resources and time, and for avoiding frustration when dealing with fixing the violations themselves.
Tools like Parasoft can be configured to detect a subset of the entire MISRA standard. This reduces the amount of noise produced from the analysis and increases focus on addressing severe violations.
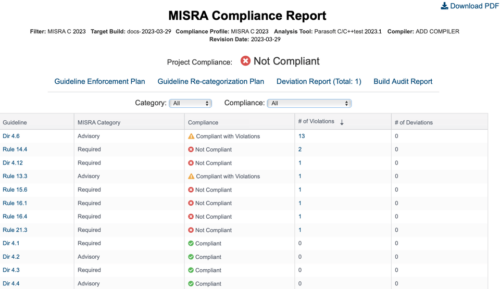
Demonstrate Compliance With Reporting
One of the problems associated with companies achieving MISRA compliance has been the absence of a standard mechanism for demonstrating compliance. To address this issue, MISRA published the previously mentioned “MISRA Compliance 2020: Achieving Compliance with MISRA Coding Guidelines.” It provides a more concrete definition of MISRA compliance and identifies several deliverables required for demonstrating compliance with the MISRA standard.
The Guideline Compliance Summary (GCS). A mandatory and primary record of overall project compliance. The GCS includes an entry for each guideline, its level of compliance, any deviations, and/or re-categorization.
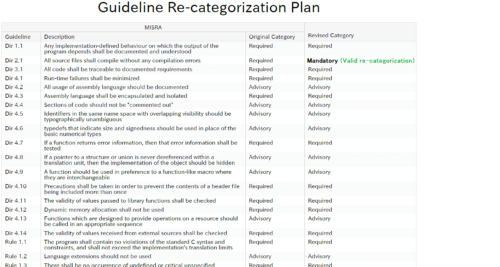
The Guideline Re-categorization Plan. All mandatory guidelines must be followed to achieve compliance. However, Required and Advisory guidelines can be re-categorized into stricter categories such as from Advisory to Required. However, only Advisory guidelines can be recategorized into less strict categories, for example from Advisory to Disapplied.
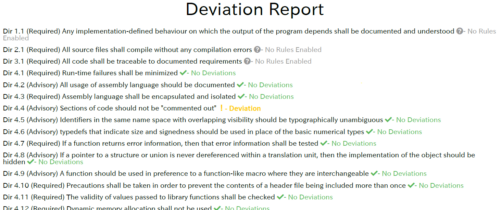
Deviations Report. Your project can have deviations from guidelines or rule violations and still be considered compliant if the deviations are justified, documented in the report, and do not impact safety.
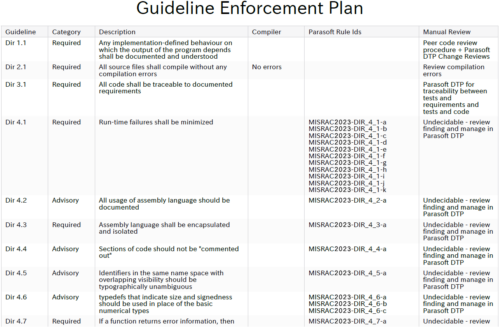
Guideline Enforcement Plan. Demonstrates how to verify each MISRA guideline. In the context of MISRA compliance with Parasoft, the GEP maps MISRA guidelines to Parasoft code analysis rules and DTP functionality.
Certified for Use on Safety-Critical Software, Including in Medical Devices
Certified by TÜV SÜD, C/C++test automates the application and monitoring of analysis coding criteria like MISRA. This includes a unit test platform that integrates creating tests and executing them, and also coverage reporting. Then the centralized analytics and reporting hub Parasoft DTP, which is also TÜV certified, aggregates and correlates analysis and test data from Parasoft C/C++test.
How to Achieve Full MISRA Compliance With Legacy Code, Including Embedded Systems
It’s a fact that developers re-use legacy code for safety-critical software. However, re-using legacy code and realizing complete MISRA C 2023 compliance can be daunting.
MISRA compliance is much easier to manage and achieve as the code is written. The MISRA C 2023 document even provides a warning that we can interpret when applying it to legacy programs:
“ … a project that checks for MISRA compliance late in its cycle is likely to spend a considerable amount of time re-coding, re-reviewing, and re-testing. It’s therefore expected that the software development process will require the early application of MISRA C principles.”
Noting reuse of legacy software, MISRA Consortium Limited, the organization responsible for creating and maintaining the MISRA standard, created MISRA Compliance:2020. This document provides guidance for developers who write new code and for those who are using adopted or legacy code.
However, the distinction may not be totally clear. For example, during product development, a coder writes software for a prototype only to find out that the project needs MISRA compliance, so he or she must backtrack and apply the guidelines.
While this is not applying MISRA to legacy code, it is similar in that when the code is scanned or analyzed, the results reveal thousands, if not tens of thousands, of violations. Add this to the fact that writers of embedded software often state that developing fully compliant code is too difficult, and the task of complying with MISRA may appear overwhelming. But finding a realistic middle ground between daunting and compliance is possible.
Consider the End Goal
MISRA Compliance 2020 helps clarify how to prove and demonstrate conformance at a project’s end. Delivering the four mandatory documents is a must. Consider the following for legacy and new code compliance.
- Have you established a GRP (Guideline Re-categorization Plan) at the project’s start? MISRA standards suggest negotiating with the client and also creating several GRPs tailored to adopted code, which developers can use without modifying, as well as for new code.
- Has the client reviewed the GPS (Guidelines Compliance Summary) templates at the project’s start? Are they complete and acceptable?
Parasoft automates the necessary reports to assist businesses in satisfying the MISRA 2020 Compliance agenda.
An Incremental Approach
It’s smart to establish a workflow to fix violations on a reasonable schedule without interrupting the development of code and therefore degrading it. Crucial recommendations include:
- Establish a baseline. After the initial scan, mark the violations as “address later,” setting this as a baseline. From that point on, when coders develop new code, maintain a strategy of “no new violations.”
- Set a deadline. Set a date after which developers must have resolved all violations for every source file.
- Prioritize based on severity. The team leader selects the violations based on how critical they are, and developers fix all of those she or he assigns them.
To make this easier, Parasoft’s DTP reporting hub includes a compliance status dashboard.
Tool Qualification
The goal of qualifying tools is to certify that they are valid for the use intended. It includes proof of how the team came to qualify them and the rationale behind it. Parasoft’s C/C++test and DTP have been TÜV SÜD certified for use on safety-critical applications. A tool qualification kit exists for some of the strictest process standards and their requirements like DO-178C.
Staff Training and Competency
The MISRA standard also stresses competency, expertise, and training of staff as key factors for evaluating product readiness. This includes recognizing the risks of violations, and properly configuring and using development tools and static analysis.
Conclusion
It’s important to support MISRA compliance throughout the software development lifecycle. Reaching compliance with MISRA is easier with Parasoft’s comprehensive solution. With ongoing enforcement, traceability, and automating documentation, teams can save time, resources, and alleviate frustrations that come with adhering to this guideline.
Learn how your development team can get the most extensive MISRA coverage.
“MISRA”, “MISRA C” and the triangle logo are registered trademarks of The MISRA Consortium Limited. ©The MISRA Consortium Limited, 2021. All rights reserved.