Discover TÜV-certified GoogleTest with Agentic AI for C/C++ testing!
Get the Details »
Jump to Section
Parasoft Blog


Application scanning is one of the best ways to detect security vulnerabilities in software. SAST is a powerful application scanning model used in several organizations. Here's a discussion on the role of Parasoft's static analysis in software scanning.
Jump to Section
Defense Information Systems Agency (DISA), Application Security and Development (ASD), and Security Technical Implementation Guides (STIG), known as DISA ASD STIG, is a technical implementation guide about application security and development for the defense information systems agency. There are many STIGs for securing different parts of DoD infrastructure and services, however, the ASD guidelines cover in-house application development and the evaluation of third-party applications.
Achieving compliance with the DISA ASD STIG guidelines requires proof, usually in the form of documentation, that satisfies auditors. This post covers:
The DISA ASD STIG provides a detailed set of guidelines for enhancing the security of software systems, primarily within the Department of Defense (DoD). The compliance authority assesses whether or not systems and software are configured to meet Defense Information Security Agency (DISA) requirements. Failure to comply with DISA STIGs can block or delay the deployment of your software.
Given the extensive nature of this compliance guideline, government agencies and defense contractors often encounter several challenges when trying to meet DISA ASD STIG compliance requirements. Some of these challenges include the following.
To achieve compliance, a three-level approach to validation is required:
This 1-2-3 punch is the key to achieving compliance by validation and documentation. The goal is to mature the process beyond detection into the prevention of security vulnerabilities.
The ASD STIG uses a severity category code (CAT I, CAT II, CAT III) to organize and prioritize the guidelines based on the possible impact of an exploit of the guideline.
Evaluating product and process documentation as well as observing and verifying functionality against the guidelines determines compliance. In other words, the STIG requires evidence of secure design and implementation through documentation, verification, and validation of all aspects of the software development lifecycle. That includes deployment and operation. These guidelines apply throughout the lifetime of the product from configuration, deployment, maintenance, and end of life.
Important to the discussion in this post is the requirement for application code scanners:
"…an automated tool that analyzes application source code for security flaws, malicious code, and back doors." —DISA ASD STIG Overview, Section 4.1
In more common terminology, this is static application security testing (SAST) implemented through static code analysis. It "should be utilized whenever possible. Particularly in the development environment where code that has been identified as requiring remediation can be addressed prior to release." The ASD STIG also contains the following guidance:
"An application scanner can be used to test development or production application systems for security vulnerabilities resulting from either application code errors or application system misconfigurations. These vulnerabilities include SQL Injection, Code Injection, Cross Site Scripting (XSS), file disclosures, permissions, and other security vulnerabilities that can be found in network accessible applications" —DISA ASD STIG Overview, Section 4.2 – Application Scanner
The ASD STIG requires the use of active vulnerability testing, for example, pen testing tools or DAST, to test executable software. These tools are required during development and deployment to support vulnerability assessments.
The ASD STIG outlines ways to verify compliance with requirements, which include:
Teams use SAST tool reports and audits to validate applications and code scanning. Functional testing is verifying with automated tools or manual testing that the vulnerability is not present in the software. In other words, think about the approach as "do something, check something". For example, check if the action worked properly and was logged if necessary). These approaches suit automated testing because of the efficiency and the audit trail tools provide.
The reality of software development for DoD, which requires DISA ASD STIG, is that you must test for all requirements and vulnerabilities. It can be a daunting task, but automation is possible to lift some of the burdens.
Parasoft’s recommendation on how to approach complying with DISA ASD STIG is to leverage automation where it makes the most sense, such as in CI/CD pipelines or DevSecOps processes. The goal is to ease the burden of compliance, use pre-emptive techniques to prevent vulnerabilities, and ultimately achieve continuous compliance.
It’s more expensive and time-consuming to detect and fix vulnerabilities when the software is almost complete versus during development. For this reason, Parasoft’s approach is to shift left assessing, detecting, and remediating vulnerabilities earlier in the life cycle.
The DISA ASD STIG uses the term "application scanning", which amounts to static code analysis and related technologies such as software composition analysis. In addition to the general requirement for vulnerability assessment via static code analysis, there are specific requirements to scan for specific vulnerabilities such as:
Although this looks like a small set of vulnerabilities, the reality is this translates into many related software weaknesses. For example, the OWASP (Open Web Application Security Project) Top 10 translates to over 50 CWEs. Each can have multiple related weaknesses.
Although this is the set of vulnerabilities specific for compliance, it’s prudent to consider a wider swath of vulnerabilities to detect. In addition, it’s important that teams expand their focus beyond the guidelines in the DISA ASD STIG to include preventative guidelines like those included in common industry secure coding standards.
As the name implies, the OWASP Top 10 is an organization committed to improving the security of web applications. Their OWASP Top 10 project provides a list of the most common and high-impact web application security vulnerabilities.
While it’s possible to use static analysis tools to detect most of the issues, some are not statically analyzable. The guideline to avoid software with known vulnerabilities is related to software composition analysis (SCA). Parasoft supports this by integrating with SCA tools with our static analysis output into a single report resulting in full Top 10 coverage.
Parasoft static analysis has out-of-the-box support for OWASP Top 10 through preconfigured settings and specific web dashboards for C/C++, Java, and C#/.NET. OWASP reporting in Parasoft DTP provides a fully auditable compliance framework for projects. The standards-specific dashboard, like the one below for DISA ASD STIG, provides an easy way to continuously monitor status.
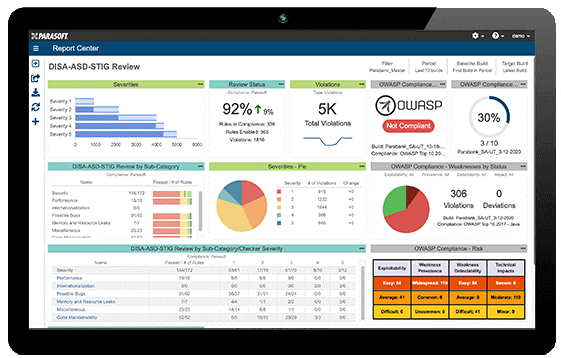
Parasoft DISA ASD STIG Dashboard
Parasoft implemented all the major application security standards, such as SEI CERT secure coding, CWE (Common Weakness Enumeration) coding guidelines, UL 2900, OWASP, and security-specific dashboards for each. This helps users understand risk and prioritization of outstanding violations/vulnerabilities/security defects.
Compliance reports are available on demand. Compliance criteria is flexible and specific to the team’s project and codebase. Developers can craft policies based on severity, risk, impact, age of code, the importance of components, and so on. They can use them to easily guide development and show efforts to an auditor. Developers can also pass policies to the security team to integrate with the results of other parts of security testing, such as the OS, network, and more.
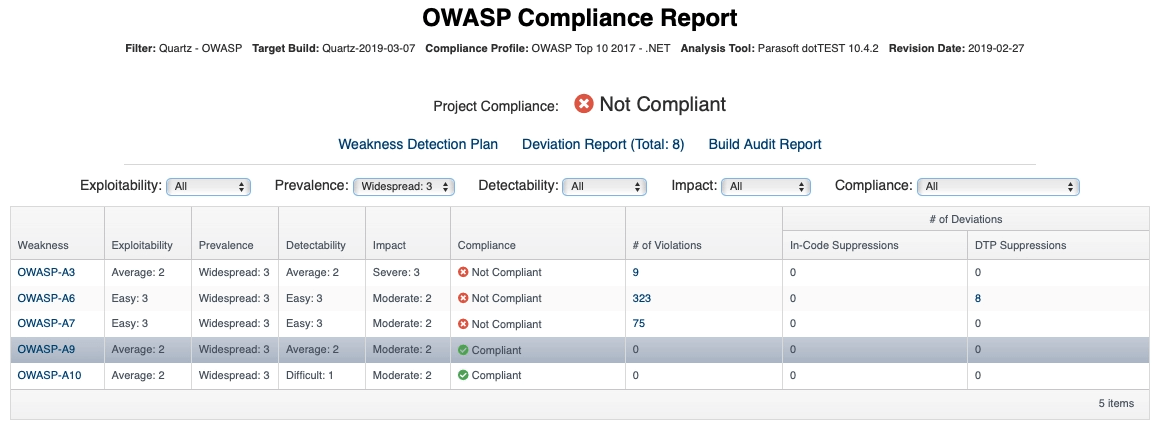
Parasoft OWASP Top 10 Compliance Report
One of the crucial aspects of static analysis tools is reporting and analytics capabilities. Projects create a large amount of data in terms of warnings and are multiplied build by build. Data management is key to the successful adoption and return on investment for static analysis tools.
Dashboards, reports, and conformance tuned for each coding standard and security guideline are critical. Parasoft analytics leverage industry-standard risk models and multiple artificial intelligence (AI) and machine learning (ML) techniques to prioritize the security warnings and help developers focus on the most critical issues with the biggest impact.
The DISA ASD STIG presents a daunting set of requirements for securing software for DoD applications. There are various methods of demonstrating compliance with the rules outlined in the STIG. The usual methods include:
The STIG outlines key areas of opportunity for automation such as application code and application scanning. Static analysis helps achieve some of these.
A pragmatic approach eases the compliance burden and encourages preventative techniques that remove vulnerabilities early in the project lifecycle. Parasoft’s static analysis provides early detection of vulnerabilities. This solution enforces code style and quality to prevent poor security practices as early as possible.